EKS を触ってみる
- EC2インスタンスを作成して、ssh でログインする。
- IAMロールを作成してEC2にアタッチする。
- eksctl をインストールする。
$ curl --silent --location "https://github.com/weaveworks/eksctl/releases/download/latest_release/eksctl_$(uname -s)_amd64.tar.gz" | tar xz -C /tmp
$ sudo mv /tmp/eksctl /usr/local/bin
$ eksctl version
[ℹ] version.Info{BuiltAt:"", GitCommit:"", GitTag:"0.13.0"} ★
$ curl -o kubectl https://amazon-eks.s3-us-west-2.amazonaws.com/1.12.7/2019-03-27/bin/linux/amd64/kubectl
$ chmod +x ./kubectl
$ mkdir -p $HOME/bin && cp ./kubectl $HOME/bin/kubectl && export PATH=$HOME/bin:$PATH
$ echo 'export PATH=$HOME/bin:$PATH' >> ~/.bashrc
$ kubectl version --short --client
Client Version: v1.12.7 ★
- aws-iam-authenticator をインストールする。
$ curl -o aws-iam-authenticator https://amazon-eks.s3-us-west-2.amazonaws.com/1.12.7/2019-03-27/bin/linux/amd64/aws-iam-authenticator
$ chmod +x ./aws-iam-authenticator
$ mkdir -p $HOME/bin && cp ./aws-iam-authenticator $HOME/bin/aws-iam-authenticator && export PATH=$HOME/bin:$PATH
$ echo 'export PATH=$HOME/bin:$PATH' >> ~/.bashrc
$ aws-iam-authenticator help
A tool to authenticate to Kubernetes using AWS IAM credentials
Usage:
aws-iam-authenticator [command]
Available Commands:
help Help about any command
init Pre-generate certificate, private key, and kubeconfig files for the server.
server Run a webhook validation server suitable that validates tokens using AWS IAM
token Authenticate using AWS IAM and get token for Kubernetes
verify Verify a token for debugging purpose
version Version will output the current build information
Flags:
-i, --cluster-id ID Specify the cluster ID, a unique-per-cluster identifier for your aws-iam-authenticator installation.
-c, --config filename Load configuration from filename
-h, --help help for aws-iam-authenticator
-l, --log-format string Specify log format to use when logging to stderr [text or json] (default "text")
Use "aws-iam-authenticator [command] --help" for more information about a command.
$ aws configure
AWS Access Key ID [None]:
AWS Secret Access Key [None]:
Default region name [ap-northeast-1]: ap-northeast-1
Default output format [None]:
$ eksctl create cluster \
--name EKS-handson \
--version 1.14 \
--nodegroup-name standard-workers \
--node-type t2.micro \
--nodes 3 \
--nodes-min 3 \
--nodes-max 5 \
--node-ami auto
$ kubectl get all
NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE
service/kubernetes ClusterIP 10.100.0.1 <none> 443/TCP 15m
$ sudo yum -y install git
$ git clone https://github.com/kubernetes/examples.git
- examples/guestbook/frontend-service.yaml を編集する。
apiVersion: v1
kind: Service
metadata:
name: frontend
labels:
app: guestbook
tier: frontend
spec:
type: LoadBalancer ★コメントアウトを外す
ports:
- port: 80
selector:
app: guestbook
tier: frontend
$ kubectl apply -f examples/guestbook
$ kubectl get pod
$ kubectl get pod
NAME READY STATUS RESTARTS AGE
frontend-69859f6796-957fl 1/1 Running 0 5m39s
frontend-69859f6796-9k487 1/1 Running 0 5m39s
frontend-69859f6796-dwphj 1/1 Running 0 5m39s
redis-master-596696dd4-l9w8n 1/1 Running 0 5m39s
redis-slave-96685cfdb-6ppw9 0/1 Pending 0 5m38s
redis-slave-96685cfdb-dkfg6 0/1 Pending 0 5m38s
$ kubectl get service
NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE
frontend LoadBalancer 10.100.26.209 a******-1******6.ap-northeast-1.elb.amazonaws.com 80:32040/TCP 8m22s
kubernetes ClusterIP 10.100.0.1 <none> 443/TCP 27m
redis-master ClusterIP 10.100.79.54 <none> 6379/TCP 8m22s
redis-slave ClusterIP 10.100.195.10 <none> 6379/TCP 8m21s
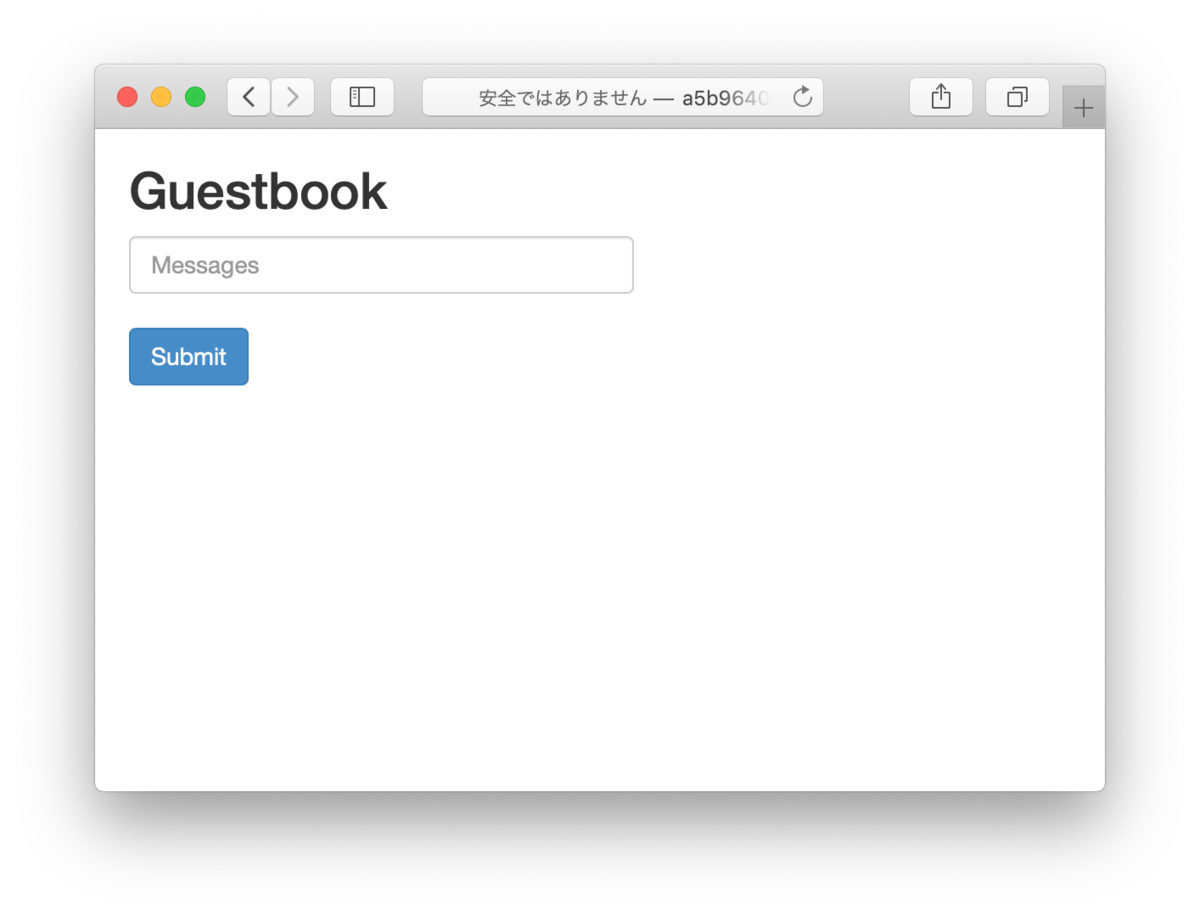
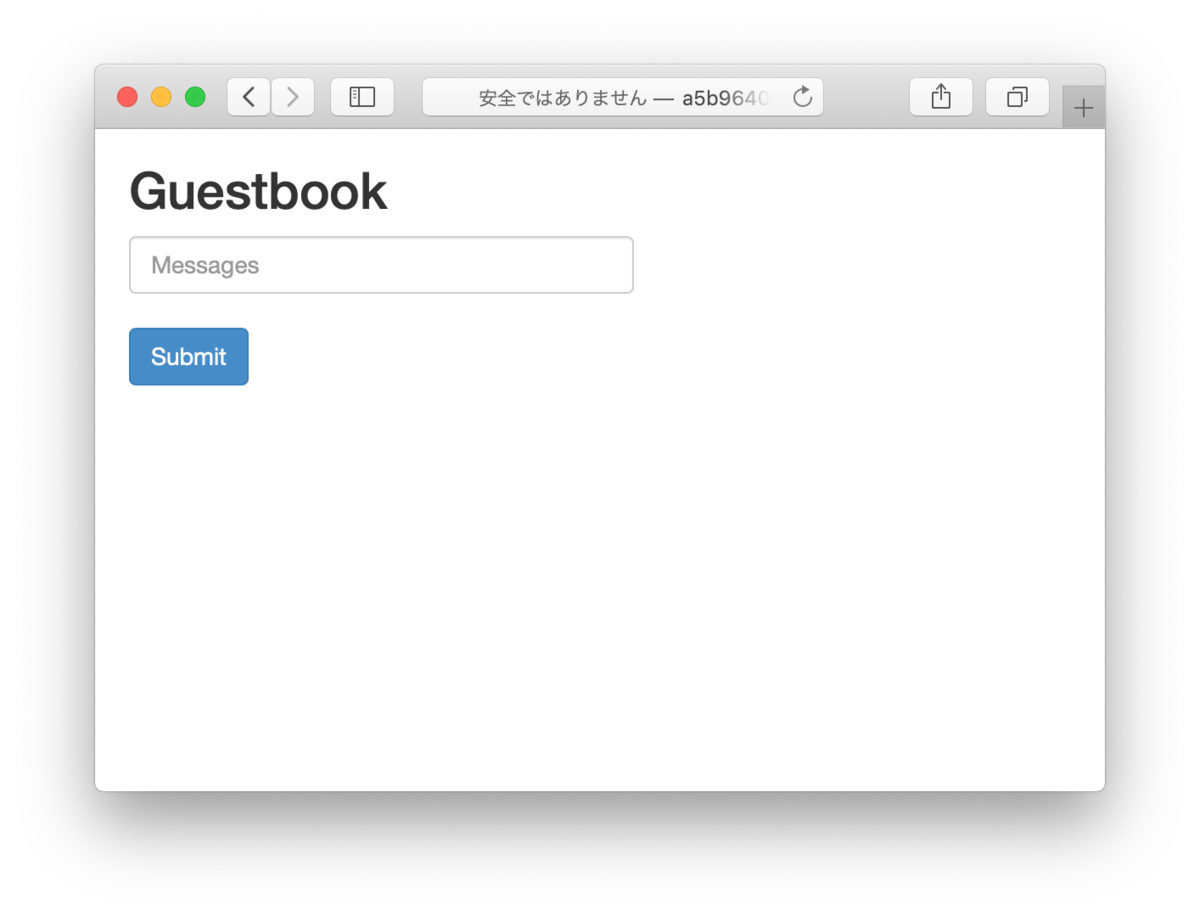
- 上記の "frontend" の URL にブラウザでアクセスする。
Fargate for EKS を触ってみる
{
"Version": "2012-10-17",
"Statement": {
"Effect": "Allow",
"Principal": {
"Service": "eks-fargate-pods.amazonaws.com"
},
"Action": "sts:AssumeRole"
}
}
$ aws iam create-role \
--role-name AmazonEKSFargatePodExecutionRole \
--assume-role-policy-document file://eks-fargate-pods-policy.json
$ aws iam attach-role-policy \
--role-name AmazonEKSFargatePodExecutionRole\
--policy-arn "arn:aws:iam::aws:policy/AmazonEKSFargatePodExecutionRolePolicy"
- マネジメントコンソールでEKSクラスターを表示し、「Faragateプロファイルを追加」をクリックし、ウイザードに従って追加する。
- name: test-profile
- Pod execution role: AmazonEKSFargatePodExecutionRole
- サブネット: パブリックサブネットは「×」を押して選択から外す。
- Namespace: default
- Pod が実行状態になっていることを確認する。
$ kubectl get pods
NAME READY STATUS RESTARTS AGE
demo-app-6dbfc49497-kzptt 1/1 Running 0 7m53s ★
frontend-69859f6796-957fl 1/1 Running 0 31m
frontend-69859f6796-9k487 1/1 Running 0 31m
frontend-69859f6796-dwphj 1/1 Running 0 31m
redis-master-596696dd4-l9w8n 1/1 Running 0 31m
redis-slave-96685cfdb-6ppw9 0/1 Pending 0 31m
redis-slave-96685cfdb-dkfg6 0/1 Pending 0 31m
- ノードを確認すると fargate が追加されている。
$ kubectl get nodes
NAME STATUS ROLES AGE VERSION
fargate-ip-192-168-170-190.ap-northeast-1.compute.internal Ready <none> 7m13s v1.14.8-eks ★
ip-192-168-5-125.ap-northeast-1.compute.internal Ready <none> 44m v1.14.8-eks-b8860f
ip-192-168-52-17.ap-northeast-1.compute.internal Ready <none> 44m v1.14.8-eks-b8860f
ip-192-168-93-205.ap-northeast-1.compute.internal Ready <none> 44m v1.14.8-eks-b8860f